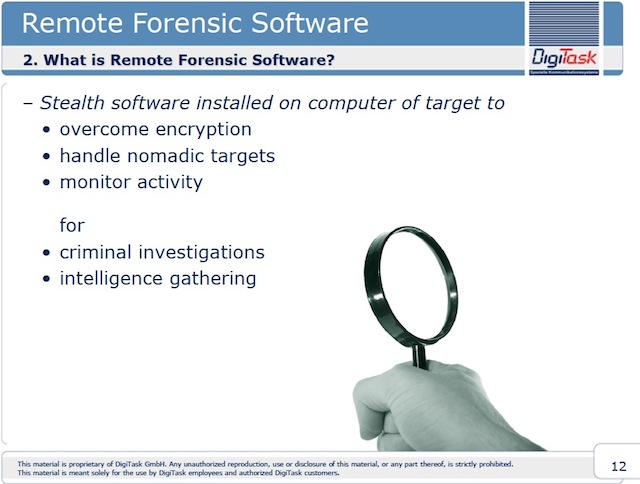
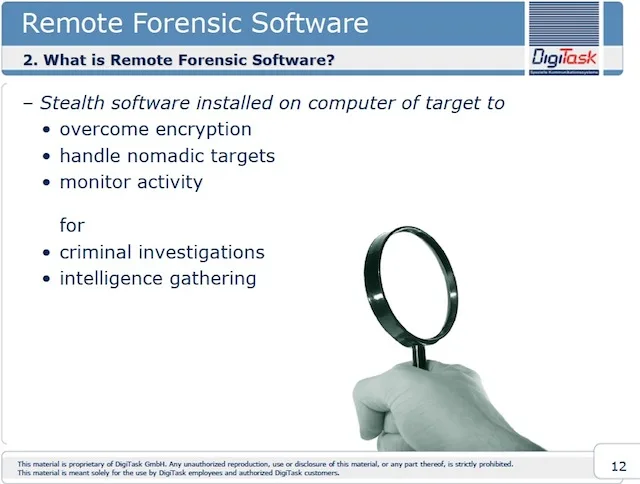
As part of the SpyFiles operation initiated by WikiLeaks, in which OWNI has been working as a partner, the names of companies that supply hacking software known as trojans to the police and intelligence services can now be revealed. These systems are introduced via hard drives, files and messages and are capable of spying in real time on unsuspecting targets. These include the German company DigiTask, who have equipped the Swiss and German police and, in a commercial brochure which OWNI has been able to consult, soberly present the trojan as a piece of “remote forensic software”. Other companies that OWNI can now name are ERA (Switzerland), whose spy systems were recently still being used in Syria; Hacking Team (Italy); and Gamma (Great Britain), through their subsidiary FinFisher (™), whose full catalogue OWNI was been able to gain access to.
As simple as a USB key
FinFisher, whose logo is a shark fin, describe themselves as a leader in the field of “offensive information gathering techniques.” While they claim to work only with intelligence and law enforcement services, FinFisher’s product portfolio makes no attempt to beat around the bush. It offers a complete range of tools for computer espionage and “remote listening, control and infection solutions” for computers, capable of “remotely taking control (and) infecting the targeted systems”, allowing the client to spy on sent or received messages and to access all of the targeted computer’s data, even if it’s encrypted.
In another presentation dating from 2007, FinFisher also boasted of “using and incorporating black hat (illegal and malicious) hacking techniques to allow intelligence services to acquire information that would be very difficult to obtain legally.”

Are you able to physically access your target computer? Simply insert the FinUSB, a small USB key created specifically to extract every ID and password contained in a computer, the most recently opened or modified files, the history of sites visited, instant messages and the contents of the trash – all without the owner noticing. All the client need do is insert the USB into the computer, under the pretext of sharing a file with the owner, and the spyware will surreptitiously siphon all the data contained within.
It’s a technique that’s already used by spies, who leave a USB stick hanging about at a trade show or in the office, hoping that their curious target will try to read it, and unwittingly infect their computer.
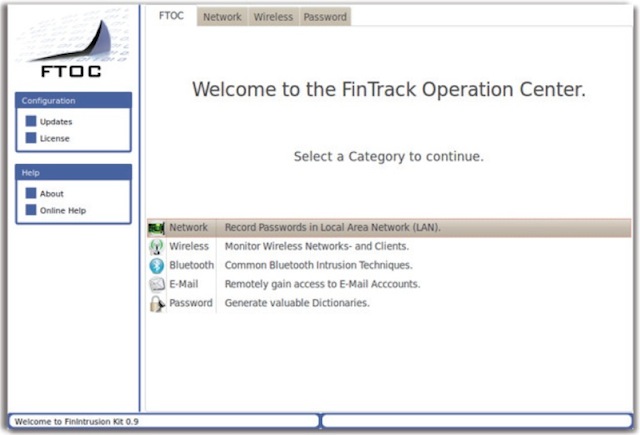
You don’t have physical access to the computer you’re spying on? No problem. “Conceived by experts working for over 10 years in the field of intrusion”, the FinIntrusion Kit penetrates the security mechanisms of wireless networks like Wi-Fi (WEP or WPA1 & 2). It also allows for the “remote monitoring of webmail (Gmail, Yahoo) and social networks (Facebook, MySpace)”, and the recovery of usernames and passwords, even if the target uses SSL, the protocol used to secure exchanges on the Internet.
FinSpy is a “Professional Trojan Horse” that has been used “for years” to facilitate placing under surveillance targets that move about regularly, encrypt their communications, connect anonymously, “and who reside in foreign countries” (FinFisher’s emphasis). FinSpy takes control, remotely and surreptitiously, of any computer using “the major operating systems like Windows, Mac and Linux”. None of the 40 most widely used antivirus systems are able to recognize it, and thus can not block it.
Once installed, FinSpy allows the client to spy “live” on the user or users of the infected computer (by activating, without their knowledge, the user’s webcam and microphone). It can also geolocate the computer, extract all of its data, intercept mail exchanges and other conversations, including calls and file transfers carried out over Skype. For the even stealthier, the connection passes remotely through anonymous proxies which prevent tracing back to the spies’ computers.
A version of FinSpy also exists for mobiles, to help authorities “who do not have a telephone interception system” to spy on communications (voice, SMS, MMS, emails) coming from mobile phones (BlackBerry, iPhone, Android or Windows ), even if those communications are encrypted. FinSpy also allows the client to access data (contacts, calendars, photos, files) stored on the mobile devices, and to geolocate them in real time.
Infected while visiting a site
FinFly is a product designed to surreptitiously install a trojan that enables the user to remotely control the computer of those suspicious types who do not click on attachments, and know more or less how to protect their computers:
It is almost impossible to infect the computers of targets who are aware of computer security issues, whose operating system is updated regularly and therefore does not have an easily exploitable security failing.
FinFlyUSB allows the client to infect a computer simply by connecting to a USB key. FinFly LAN (Local Area Network) offers to do the same, but without the necessity of physical access to the target computers, by infiltrating a network (cable or Wi-Fi, including those found in Internet cafes or hotels). FinFly ISP (Internet Service Provider) takes this process to an even greater extreme, infiltrating the ISP itself in order to deploy spyware “on a national scale.”
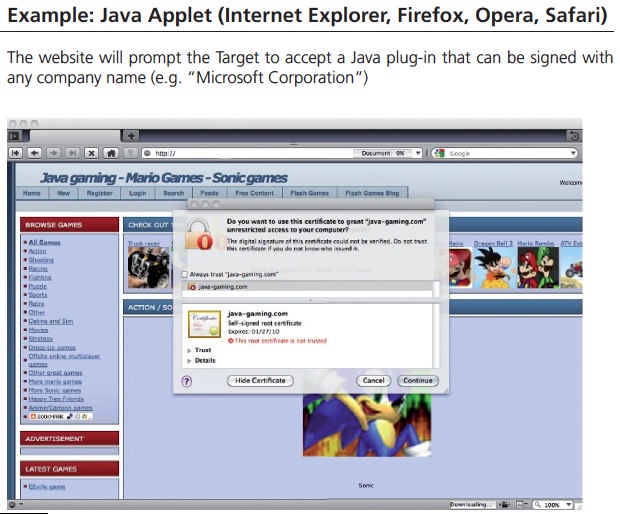
In both cases, the goal is to infect “on the fly” the files that the targets are currently downloading by sending false infected security updates; or to “manipulate” web pages the target visits in order to deploy a trojan. This means that a single web page can contaminate the computers of all of those who visit it. To achieve this, FinFisher developed FinFly Web. FinFisher further explain how “targets” have been spied on as a result of their visiting a website created specifically to attract their attention.
The portfolio also explains how it’s possible to convince the target user that they need to download a file (a Flash or RealPlayer plug-in, a Java applet, etc) that’s been duly signed by a well-known company – “Microsoft, for example.” This would suggest that either these companies are working with FinFisher, or FinFisher have managed to hack into their security certificates in order to allow them to guarantee the authenticity of the downloaded files.
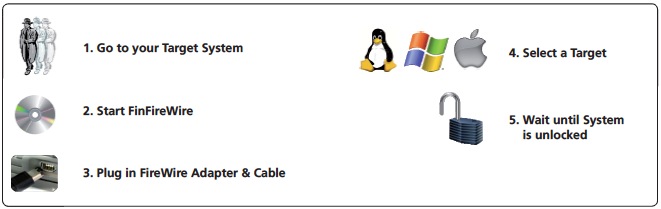
FinFireWire makes it possible to access the contents of computers (Windows, Mac and Linux) whose access is protected by a password, without leaving a trace. The FinFisher portfolio even specifies that it allows the client to spy without judicial supervision, citing the case of police entering the apartment of a suspect whose computer, switched on, is protected by a password:
To the extent that they are not permitted, for legal reasons, to install a trojan on the computer (of the suspect), they risk losing all the data by turning off the computer, if the hard drive is fully encrypted. FinFireWire allows them to unlock the suspect’s computer and copy all the files before turning it off and bring it back to headquarters.
“Cyber War” just a click away
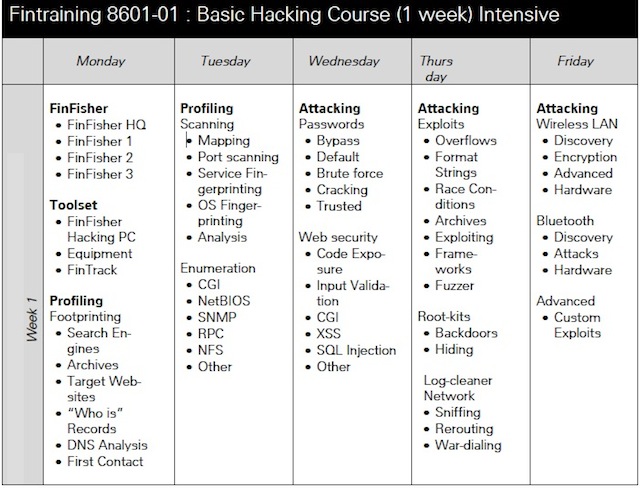
FinFisher also offer “FinTraining” to teach their clients how, “for example”: to trace anonymous emails; to remotely access webmail accounts; to familiarise themselves with wireless intrusion; “to attack critical infrastructure”; to “sniff” usernames, IDs, passwords and data transmitted over networks, including Wi-Fi hotspots in cafes and hotels; to intercept phone calls (VOIP and DECT); to crack passwords and various other “cyberwar” techniques.
Gamma Group, the British parent company of FinFisher, presents itself as a supplier of systems and technologies for the interception of telecommunications (Internet, satellite, Thuraya, Inmarsat, GSM, GPRS, SMS, etc.) for the benefit of government agencies and law enforcement. They also sell micro-spying devices and hidden micro surveillance cameras, interception vans and tools to pick open any door.
Founded in 1990 and with offices in Munich, Dubai, Johannesburg, Jakarta and Singapore, Gamma never fail to mention wherever they can that they refuse to sell these systems to non-democratic countries, or countries with a poor human rights record.
In April, The Wall Street Journal revealed that documents discovered at the headquarters of the “Electronic Penetration Department” of the Egyptian secret police, showed that FinFisher spyware had indeed been used to spy on political activists. It explained in particular the importance of using Skype “because it can not be penetrated by any security device”.
Basem Fathi, a 26 year old Egyptian activist, has discovered that the Egyptian security services had files on everything from her love life to her trips to the beach. “I think they collected all the little details which they had heard us talking about, before saving them to files,” she said.
A “top secret” memo from the Egyptian Interior Ministry dated January 1, 2011, which the WSJ was able to gain access to, reveals that the Egyptian authorities had paid €388,604 to test the spyware for five months, and could call on the support of four employees of Gamma’s Egyptian retailer, Modern Communication Systems. This allowed them to spy on many activists, including the “successful penetration of their meetings…even if they were encrypted by Skype.”
The Egyptians were not alone in being spied on. Documents have also revealed that the conversations of Sherif Mansour, a representative of the American NGO Freedom House, who had come to Egypt to monitor elections, had also been intercepted. Aware of interference from the authorities, Mansour had set up a “security protocol which mentioned using Skype as often as possible”, on the grounds that it was more secure than emails.
When questioned by the WSJ, Mr Mansour said he was surprised. “When they detained bloggers, they tortured them for their passwords,” he said. “So we had the impression they could not spy on our conversations.”
In December 2010, following this trial period, a satisfied Interior Ministry approved the purchase of the Gamma software. Only the subsequent Arab Spring and the Egyptian revolution prevented the purchase from going through.

Follow our full coverage of the Spy Files :
- How Gaddafi Spied on the Fathers of the New Libya
- Interactive Map: The United Nations of Surveillance
- SpyFiles: Revelations of a Billion-Dollar Mass Surveillance Industry
Read more of our articles about WikiLeaks
@manhack (on Twitter), jean.marc.manach (on Facebook & Google+) .
You can also contact me securely via my GPG / PGP key (which, for the uninitiated, is not very complicated). If not, and to contact me anonymously and confidentially, you can also go through privacybox.de (do not forget to leave me a valid – but anonymous – email address – so I can reply to you).
All of OWNI’s projects with WikiLeaks are here


💬 Discussion
No comments yet. Be the first to comment!